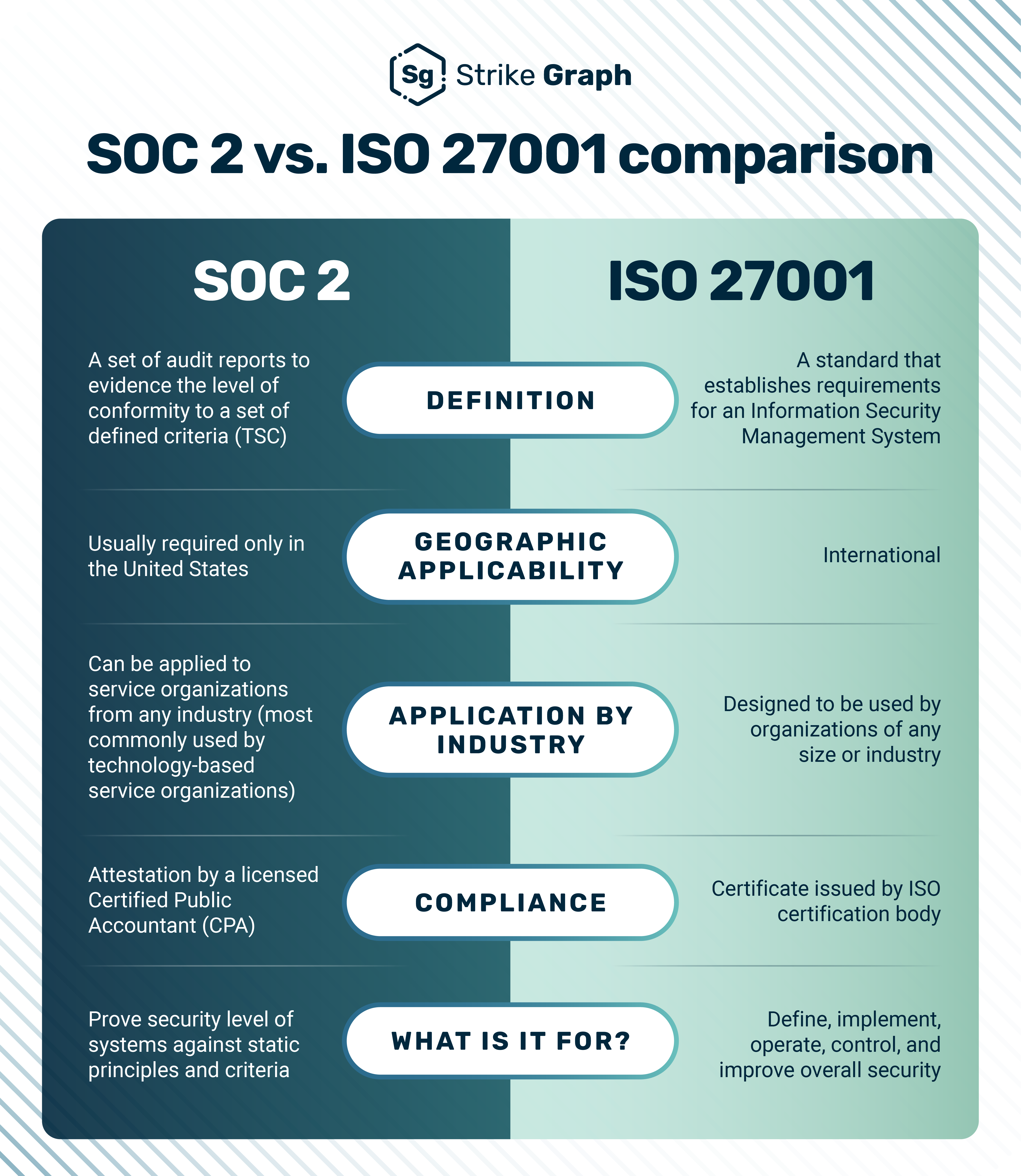
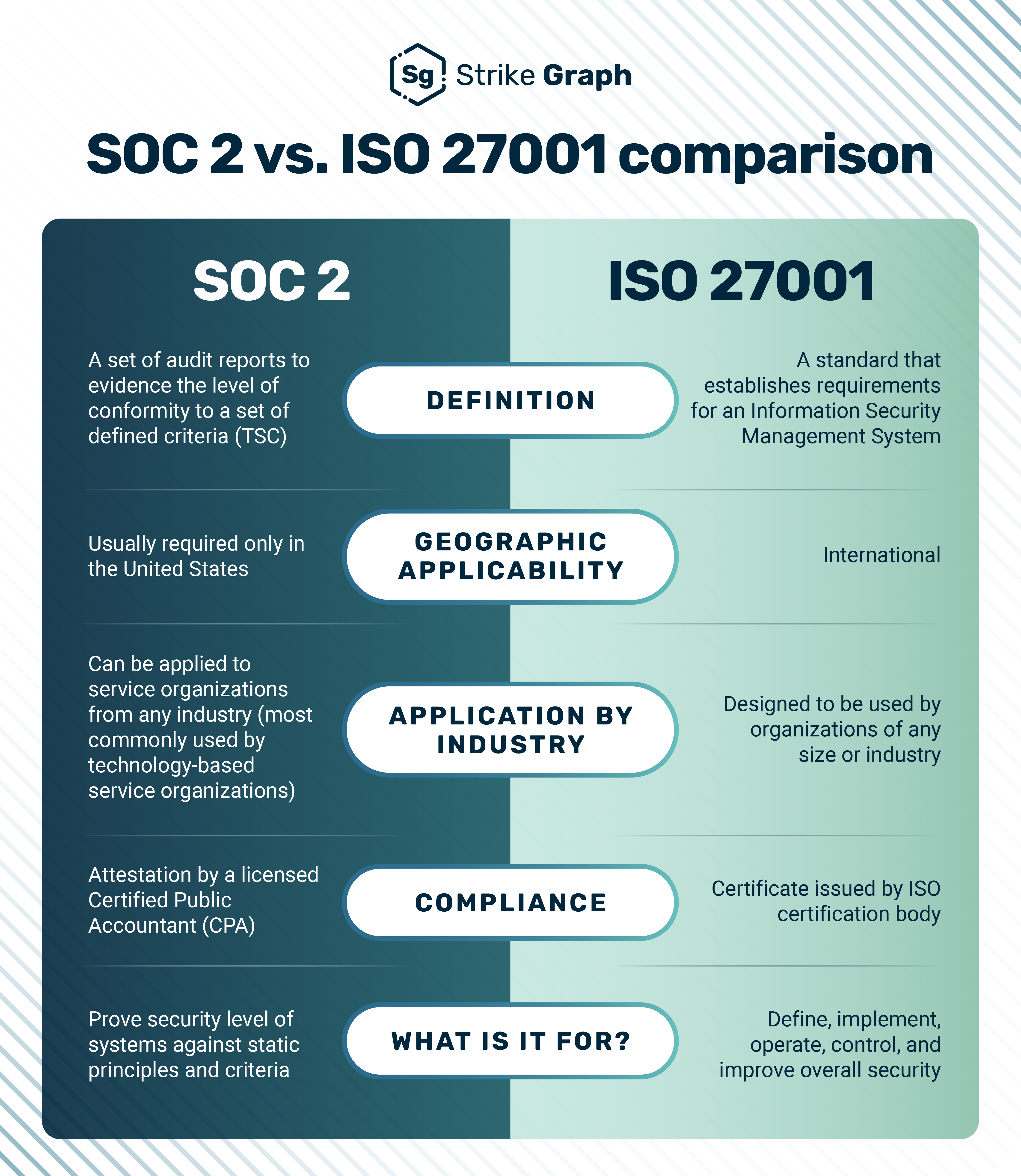
The main difference is that SOC 2 primarily focuses on proving you've implemented security controls that protect customer data. ISO 27001 also asks you to prove you have an operational information security management system (ISMS) in place to manage your InfoSec program on a continual basis.
Therefore, if you're deciding between a SOC 2 audit and an ISO 27001 certification, the easy answer is to pick the one your customer wants! Both the SOC 2 and ISO 27001 security frameworks are well respected. Both have a similar audience: end users who want to ensure that your organization has controls or programs in place to protect the security, confidentiality, and availability of data. This article will give you the tools and knowledge you need to decide.
What is SOC 2?
SOC 2, which stands for Service and Organization Controls 2, is a report that certifies a service organization’s customer data safety. An independent CPA evaluates the organization's handling of security, confidentiality, availability, processing integrity, and privacy. They provide an attestation report. US clients often require SOC 2.
Differences between SOC 2 Type 1 and Type 2
A SOC 2 Type 1 attestation report focuses on an organization’s IT security control design at a point in time. In contrast, SOC 2 Type 2 assesses the design and operating effectiveness of the controls over a specified lookback period, typically six months to a year.
A highly organized and prepared company could complete Type 1 attestation in as little as 45 days. Type 2 attestation, on the other hand, can take two to six months, depending on the organization's IT maturity, staff involvement, and other factors.

What is ISO 27001?
ISO 27001 is a globally recognized data security certification from the International Organization for Standardization (ISO). An auditor evaluates whether an organization’s information security management system (ISMS) meets the strict controls framework set by ISO. Doing business outside the US often requires ISO compliance.
How did ISO/IEC 27001:2022 change from ISO/IEC 27001:2013?
ISO/IEC 27001:2022 was released in 2022 to match the Annex SL structure of other ISO standards, making it easier to coordinate with them. It has simplified sections and updated controls to reflect current best practices and technology. ISO/IEC 27001:2022 adds new controls for cybersecurity threat intelligence, cloud security, and data privacy.
What are the similarities between ISO 27001 and SOC 2?
ISO 27001 and SOC 2 are data security compliance frameworks that are well respected in the US and share many of the same security controls. Independent auditors or assessors conduct evaluations for both. Compliance with either instills customer trust.
Here’s a list of the similarities between ISO 27001 and SOC 2:
- Both are well-respected in the USA.
- Both certifications instill trust in clients that your organization will protect their data.
- They have many security controls in common. Potentially, 80% to 100% of SOC 2 controls can map to ISO 27001 Annex A controls.
- Both are risk-based approaches to IT security.
What are the differences between ISO 27001 and SOC 2?
The main differences between ISO 27001 and SOC 2 revolve around their approaches. Both evaluate security controls, but ISO 27001 also focuses on an organization’s information security management system and requires ongoing management.
Here are the differences between ISO 27001 and SOC 2:
- ISO 27001 is more accepted internationally, while SOC 2 is more limited to the US
- Both certifications require proof that you have the security controls to protect customer data in place. ISO 27001 also wants you to prove that you have an operational ISMS.
- Depending on a company’s starting point, ISO 27001 certification usually requires more time and resources than SOC 2.
- A licensed CPA firm attests to SOC 2, while an accredited ISO registrar certifies ISO 27001.
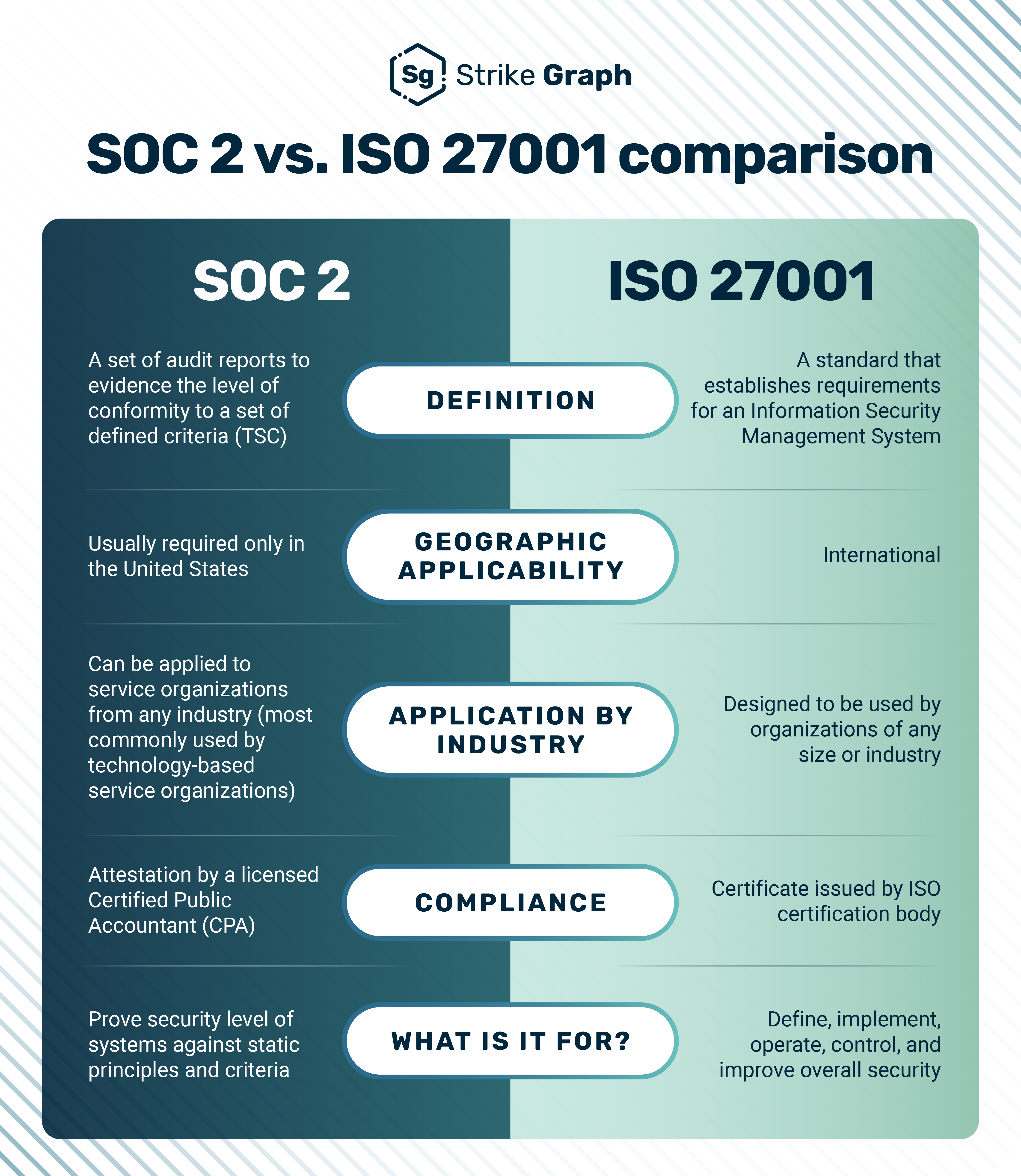
Comparing the scope of SOC 2 and ISO 27001
SOC 2 focuses on service organizations handling customer data. It emphasizes data security but may include availability, processing integrity, confidentiality, and privacy. In contrast, regardless of size or industry, ISO 27001 applies to any organization. It provides a comprehensive framework for an information security management system.
SOC 2 vs. ISO 27001
SOC 2:
- Focuses on service organizations, particularly those handling customer data
- Emphasizes security, availability, processing integrity, confidentiality, and privacy
- Customizable controls for audit flexibility
- Suitable for smaller or younger organizations
ISO 27001:
- Applicable to any organization, regardless of size or industry
- Comprehensive framework for establishing and improving an ISMS
- Rigid program implementation and maintenance requirements to manage information security risks
- Extensive certification process takes anywhere from two months to two years or more, depending on the organization’s existing setup and resources.
 Michelle Strickler, Lead Product & Compliance Experience Strategist at Strike Graph, says each standard can present challenges without proper understanding and guidance. She holds a Certified Information Systems Auditor (CISA) and Risk and Information Systems Controls (CRISC) certification and has over 15 years of experience in governance, risk, and compliance.
Michelle Strickler, Lead Product & Compliance Experience Strategist at Strike Graph, says each standard can present challenges without proper understanding and guidance. She holds a Certified Information Systems Auditor (CISA) and Risk and Information Systems Controls (CRISC) certification and has over 15 years of experience in governance, risk, and compliance.
“The biggest challenge I see with ISO is not reading the actual ISO 27001 document and missing the program needs to be maintained,” Strickler says. “Also, don’t get too wrapped up in having the ISMS be perfect out of the gate – it doesn't need to be. It can always be improved upon, and actually showing evidence of continuous improvement to an assessor or internal auditor is a bonus.”
ISO 27001's rigid program management requirements integrate various information security risks and involve a more extensive certification process. The customizable controls in SOC 2 allow organizations to tailor their audit, making it more suitable for smaller or younger organizations. Learn more about controls and see examples.
Stricker adds, “For SOC 2, the most common implementation challenge is a checklist approach. This can lead to wasted time spent running controls that don't matter, pulling evidence that is unreasonable, and creating policies and procedures that are irrelevant.”
SOC 2 vs. IS0 27001 mapping
The chart below shows how SOC 2 controls can map directly to many ISO 27001 controls. Mapping the security controls instead of the standards depicts the work that goes into SOC 2 often applies to ISO 27001. This is something a business should know if it wants both certifications now or eventually.
Name of Control
|
SOC 2:2017 (2022) Reference #
CC: common controls/security,
c: continuity, pi: process integrity,
p: privacy, a: availability
|
ISO 27001:2022 Reference #
|
|
Acceptable Use Policy
|
CC 1.1
|
Annex A.5.4, Annex A.5.10, Annex A.5.32, Annex A.8.23
|
|
Administrator Access
|
CC 6.2, CC 6.3
|
Annex A.5.15, Annex A.5.34
|
|
Antivirus
|
CC 6.7, CC 6.8
|
Annex A.5.32
|
|
Antivirus Maintenance
|
CC 7.2
|
Annex A.8.16
|
|
Asset Decommission Checklist
|
CC 6.5
|
Annex A.5.11, Annex A.7.14, Annex A.8.10
|
|
Asset Inventory
|
CC 2.1, CC 6.1, C 1.1
|
Annex A.5.9, Annex A.5.13, Annex A.5.32, Annex A.8.8
|
|
Audit Trail & Logs
|
CC 6.8, CC 7.2
|
Annex A.5.15, Annex A.8.4, Annex A.8.15, Annex A.8.16, Annex A.8.18
|
|
Automatic Patching
|
CC 8.1
|
Annex A.8.19
|
|
Background Check
|
CC 1.4
|
Annex A.6.1
|
|
Backup Schedule
|
CC 7.5, A 1.2, PI 1.5
|
Annex A.8.13
|
|
Business Continuity
|
CC 8.1, CC 9.1, A 1.2, A 1.3
|
Annex A.5.21, Annex A.5.29, Annex A.5.30
|
|
Business Impact Analysis
|
CC 3.2
|
Annex A.5.29, Annex A.5.30
|
|
Capacity Planning
|
A 1.1
|
Annex A.8.6
|
|
Change Management Policy
|
CC 5.2, CC 6.1, CC 6.8, CC 8.1
|
Annex A.8.9, Annex A.8.25, Annex A.8.26, Annex A.8.29, Annex A.8.32
|
|
Change Management Procedures
|
CC 8.1, A 1.1
|
Annex A.8.26, Annex A.8.29, Annex A.8.32
|
|
Change Restrictions
|
CC 7.1
|
Annex A.8.9
|
|
Cloud Change Monitoring
|
CC 4.1, CC 7.1, CC 7.2
|
Annex A.8.16
|
|
Configuration Standards
|
CC 7.1, CC 8.1
|
Annex A.8.27
|
|
Contacting Company
|
P 8.1
|
Annex A.5.34
|
|
Contract - Secure Transmission
|
CC 9.2
|
Annex A.5.34
|
|
Contracts
|
CC 2.3, CC 9.2, P 6.1, P 6.4
|
Annex A.5.20, Annex A.5.31
|
|
Data Anonymization
|
P 4.2, P 4.3
|
Annex A.8.11
|
|
Data Center Access Review
|
CC 6.4
|
Annex A.5.18
|
|
Data Center Physical Access
|
CC 6.4
|
Annex A.7.2
|
|
Data Collection
|
P 3.1
|
Annex A.8.11
|
|
Data Flow Diagram
|
CC 2.1, CC 2.2, CC 6.1
|
Annex A.5.34
|
|
Data Loss Prevention
|
CC 6.7, C 1.1
|
Annex A.8.12
|
|
Data Management Policy
|
CC 6.5, C 1.1, C 1.2, P 4.2, P 4.3
|
Annex A.5.14, Annex A.5.33
|
|
Data Protection Officer
|
CC 1.3
|
Annex A.5.34
|
|
Data Replication
|
A 1.2
|
Annex A.8.14, Annex A.8.20
|
|
Data Retention/Deletion
|
CC 6.5, C 1.1, C 1.2, P 3.2, P 4.2, P 4.3
|
Annex A.5.14, Annex A.5.33, Annex A.5.34, Annex A.8.10
|
|
Disciplinary Process
|
CC 1.5
|
Annex A.5.4, Annex A.6.4, Clause.7.3
|
|
Disk Encryption
|
CC 6.1
|
Annex A.8.1
|
|
DMZ Network Gateway
|
CC 6.1, CC 6.6
|
Annex A.8.16
|
|
Edit Checks
|
PI 1.1, PI 1.2, PI 1.3
|
Annex A.8.11
|
|
Employee Shared Drive
|
CC 2.2
|
Annex A.5.1, Annex A.5.37, Clause.5.2, Clause.7.5.3
|
|
Encryption at Rest
|
CC 6.1, PI 1.5
|
Annex A.5.34
|
|
Encryption in Transit
|
CC 6.1, CC 6.7, PI 1.4
|
Annex A.8.24
|
|
Encryption Key Protection
|
CC 6.1
|
Annex A.8.11, Annex A.8.24
|
|
Environmental Monitoring
|
A 1.2
|
Annex A.7.5
|
|
Environmental Risk
|
A 1.2
|
Annex A.7.5, Clause.8.2
|
|
Environmental Security Policy
|
A 1.2
|
Annex A.7.5
|
|
Fire Suppression
|
A 1.2
|
Annex A.7.5, Annex A.7.8
|
|
Firewall Alerting
|
CC 6.6, CC 7.1, CC 7.2
|
Annex A.8.16, Annex A.8.21
|
|
Firewall Rules
|
CC 6.6
|
Annex A.6.7, Annex A.8.20, Annex A.8.23
|
|
Generators
|
A 1.2
|
Annex A.7.11
|
|
Hardening Standards
|
CC 7.1
|
Annex A.8.9., Annex A.8.19
|
|
HVAC Testing
|
A 1.2
|
Annex A.7.5
|
|
Incident Response: Employee Responsibility
|
CC 2.2, CC 7.3, CC 7.4, P 8.1
|
Annex A.5.24, Annex A.6.8
|
|
Incident Response: Process
|
CC 2.3, CC 7.3, CC 7.4, CC 7.5
|
Annex A.5.25, Annex A.5.26, Annex A.5.27, Annex A.5.28, Annex A.6.8
|
|
Incident Response: Responsibility
|
CC 2.2, CC 7.4
|
Annex A.5.24
|
|
Incident Response: Testing
|
CC 7.4, CC 7.5
|
Annex A.5.24
|
|
Information Security Oversight
|
CC 2.2
|
Annex A.5.1, Clause.5.1
|
|
Information Security Policy
|
CC 5.3
|
Annex A.5.1, Clause.5.1, Clause.5.2
|
|
Internal Audit
|
CC 4.1
|
Annex A.5.35, Annex A.5.36, Annex A.8.34, Clause.9.2.1, Clause.9.2.2
|
|
Intrusion Detection
|
CC 4.1, CC 6.6, CC 7.1, CC 7.2
|
Annex A.8.16
|
|
Lawful Basis
|
P 3.1, P 3.2, P 4.1, P 7.1
|
Annex A.5.34
|
|
Logical Access
|
CC 5.2, CC 6.1, CC 6.3
|
Annex A.5.15, Annex A.5.18, Annex A.8.2, Annex A.8.3, Annex A.8.5
|
|
Malware Scans
|
CC 6.8
|
Annex A.6.7, Annex A.8.7
|
|
Management Responsibilities in Policies
|
CC 5.3
|
Annex A.5.2
|
|
Media Disposal
|
P 4.3
|
Annex A.7.14
|
|
MFA for Sensitive Access
|
CC 6.1
|
Annex A.8.5
|
|
Mobile Device Policy
|
CC 6.7
|
Annex A.7.9, Annex A.8.1
|
|
Monitoring
|
CC 4.1, CC 7.2
|
Annex A.5.24
|
|
Multi-Factor Authentication
|
CC 6.6
|
Annex A.8.5
|
|
Network Diagram
|
CC 2.1, CC 2.2
|
Annex A.8.14, Annex A.8.20, Annex A.8.22
|
|
Non-Disclosure Agreement
|
CC 9.2
|
Annex A.5.4, Annex A.6.6
|
|
Organization Segregation of Duties
|
CC 1.3, CC 5.1
|
Annex A.5.3
|
|
Organizational Chart
|
CC 1.3
|
Clause.5.1
|
|
Password Requirements
|
CC 6.2
|
Annex A.5.17, Annex A.8.5
|
|
Patch Management
|
CC 7.1
|
Annex A.8.19
|
|
Penetration Test
|
CC 4.1
|
Annex A.8.8
|
|
Physical Access Policy
|
CC 6.4
|
Annex A.5.15, Annex A.7.1
|
|
Physical Access Review
|
CC 6.4
|
Annex A.5.15
|
|
Planned Maintenance
|
CC 2.2
|
Annex A.7.13
|
|
Policy Review
|
CC 5.3
|
Annex A.5.1, Clause.7.5.2
|
|
Power Supply Testing
|
A 1.2
|
Annex A.7.5, Annex A.7.11
|
|
Privacy Notice
|
CC 2.3, P 1.1, P 2.1, P 3.1, P 6.7
|
Annex A.5.34
|
|
Privacy Policy
|
P 6.1, P 6.7, P 5.1
|
Annex A.5.34
|
|
Privileged Access
|
CC 6.1, CC 6.2
|
Annex A.8.2
|
|
Production Data Restrictions
|
CC 8.1
|
Annex A.8.33
|
|
Provisioning
|
CC 6.1, CC 6.2, CC 6.3, CC 6.4
|
Annex A.5.15, Annex A.5.16, Annex A.5.18
|
|
Raised Flooring
|
A 1.2
|
Annex A.7.8
|
|
Removable Media
|
CC 6.7
|
Annex A.7.7, Annex A.7.10, Annex A.8.1
|
|
Restore
|
CC 7.4, CC 7.5, A 1.3
|
Annex A.8.13
|
|
Restrict Data Transmission
|
CC 6.7
|
Annex A.8.1
|
|
Restrict Software Install
|
CC 6.8
|
Annex A.8.1, Annex A.8.7, Annex A.8.19
|
|
Review Privileged Access
|
CC 6.2, CC 6.3
|
Annex A.5.18, Annex A.8.2
|
|
Risk Assessment Action Plans
|
CC 3.2, CC 5.1
|
Clause.8.2, Clause.8.3, Clause.6.1.3
|
|
Risk Assessment Methodology
|
CC 3.1, CC 3.2, CC 3.3, CC 3.4, CC 5.1, CC 9.2
|
Annex A.5.12
|
|
Risk Assessment Policy
|
CC 3.2
|
Clause.6.1.1
|
|
Role Based Access
|
CC 6.3
|
Annex A.5.15, Annex A.5.34
|
|
Secrets Management
|
CC 6.1
|
Annex A.5.17
|
|
Security Training
|
CC 2.2
|
Annex A.5.4, Annex A.5.24, Annex A.6.3, Annex A.8.7, Annex A.8.23, Clause.7.3
|
|
Separation of Duties: Developers
|
CC 8.1
|
Annex A.8.4
|
|
Separation of Environments
|
CC 8.1
|
Annex A.8.31
|
|
Server Racks
|
A 1.2
|
Annex A.7.5, Annex A.7.8
|
|
Server Room
|
CC 6.4
|
Annex A.7.2, Annex A.7.3, Annex A.7.8
|
|
Smoke Detectors
|
A 1.2
|
Annex A.7.5
|
|
Software Install Scan
|
CC 7.1
|
Annex A.8.1, Annex A.8.7
|
|
Software Updates
|
CC 6.8, CC 7.2
|
Annex A.5.32
|
|
Tech Competence
|
CC 1.4, CC 4.1, CC 5.3
|
Clause.7.2
|
|
Temporary Files
|
P 4.3
|
Annex A.5.34
|
|
Termination of Access
|
CC 6.2, CC 6.3, CC 6.4
|
Annex A.5.11, Annex A.5.16, Annex A.5.18
|
|
Third-Party SOC 2 Reviews
|
CC 9.2
|
Annex A.5.19, Annex A.5.22
|
|
Threat Intelligence
|
CC 3.2, CC 7.2
|
Annex A.5.7
|
|
User Access Review
|
CC 5.2, CC 6.2, CC 6.3
|
Annex A.5.15, Annex A.5.18
|
|
User Authentication
|
CC 6.1
|
Annex A.8.5
|
|
Vendor Due Diligence
|
CC 3.4, CC 9.2, P 6.4
|
Annex A.5.19, Annex A.5.21
|
|
Vendor Management Policy
|
CC 3.2, CC 9.2, P 6.4
|
Annex A.5.19, Annex A.5.32
|
|
Vendor Review
|
CC 9.2, P 6.4
|
Annex A.5.22, Annex A.8.21
|
|
Vendor Risk Register
|
CC 3.2, CC 3.4, CC 9.2
|
Annex A.5.19, Annex A.5.21
|
|
Virtual Private Network
|
CC 6.1, CC 6.6
|
Annex A.6.7
|
|
Virtual Private Network Encryption
|
CC 6.6
|
Annex A.6.7
|
|
Vulnerability Scan
|
CC 4.1, CC 6.8, CC 7.1, CC 7.2
|
Annex A.8.8
|
|
Wireless Access Points
|
CC 6.6
|
Annex A.8.20
|
|
Wireless Networks
|
CC 6.1
|
Annex A.8.22
|
|
Workstation Lockout
|
CC 6.7
|
Annex A.8.1
|
Download ISO 27001 vs. SOC 2 mapping in Excel
Which framework should your company adopt?
Adopting ISO 27001 or SOC 2 depends on your organization’s needs and objectives. ISO 27001 is an internationally recognized framework ideal for systematically managing information security risks. SOC 2 is for service organizations needing to demonstrate their commitment to data security, especially to US-based clients.
When approaching this question, Strickler suggests, “First, consider your buyers' preferences. If an ISO 27001 certification is contractually required and a SOC 2 is not, follow the contract. SOC 2 can be a fantastic entry-level framework as it is risk- and controls-based. ISO 27001 builds on risks and controls and introduces a more robust program for security that needs to be managed. The cost of ISO 27001 compliance is slightly higher, both in audit and certification cost and in the hidden cost of the staff of maintaining a program.”
 Stephen Ferrell, Chief Strategy Officer at Strike Graph and the holder of CISA and CRISC certifications, adds that geography is often a big factor in the choice. “If you are a US company with US-centric customers, SOC is probably going to be your pick. If you are a more global organization, ISO 27001 is a better bet because it's recognized widely outside the US. Some European and UK companies will ask for SOC 2, but I would say they're in the minority.”
Stephen Ferrell, Chief Strategy Officer at Strike Graph and the holder of CISA and CRISC certifications, adds that geography is often a big factor in the choice. “If you are a US company with US-centric customers, SOC is probably going to be your pick. If you are a more global organization, ISO 27001 is a better bet because it's recognized widely outside the US. Some European and UK companies will ask for SOC 2, but I would say they're in the minority.”
When is ISO 27001:2022 a good choice?
ISO 27001:2022 is an excellent choice for international businesses seeking a systematic approach to managing information security. It is well-suited for companies handling sensitive information that need a structured framework to address data security risks comprehensively.
Consider these aspects of ISO 27001:
- Global reach: Ideal for organizations with international clients or operations.
- Comprehensive framework: Suitable for establishing and maintaining a robust ISMS.
- Client requirements: Necessary if clients demand ISO 27001 certification.
- Long-term strategy: Fits companies ready to invest in a detailed and ongoing security management process.
While ISO enables business opportunities outside the US, companies need to be ready for the implementation work. “Implementation is very involved, and then there’s the maintenance of it,” Strickler explains. “It’s just not a one-and-done. Your choice depends on a few things: How mature is the organization? How big is it? Are there subsidiaries that are cross nationalities and borders?”
Strickler says ISO's additional requirements may overload less mature companies. “ISO actually mandates that you establish an information security management system. If you don't have the bandwidth or staff to tackle that, it can be very disruptive for smaller organizations focused on revenue and growth.”
When is SOC 2 a good choice?
SOC 2 is well-suited for businesses that handle customer data and must demonstrate data protection measures to US-based clients. Selecting controls is more flexible, and you can tailor it to meet your needs, making it a practical choice for younger companies.
Consider these aspects of SOC 2:
- US market focus: Best for companies primarily serving US clients.
- Customizable controls: Select specific controls, which is beneficial for smaller or newer organizations.
- Building trust: Essential for service providers needing to prove their security measures to clients.
- Faster compliance: A quicker path to certification, with SOC 2 Type 1 provides a quicker path to certification, is achievable in as little as 45 days.
Strickler likens the SOC 2 framework to “choose-your-own-adventure books,” especially compared to the highly prescriptive ISO framework. This option enables startups or other smaller organizations to choose what they need most. Often, a contract that requires SOC 2 attestation is the impetus for getting it.
When should companies do both ISO 27001:2022 and SOC 2
Companies should consider obtaining both ISO 27001:2022 and SOC 2 certifications when they have a presence in international and US markets and must meet diverse client requirements. Combining both frameworks is a robust approach to information security management and enhances.
Consider these aspects of having both certifications:
- International and US presence: Suitable for companies operating globally and in the US.
- Meeting diverse client needs: Necessary for organizations serving clients with different certification requirements.
“SOC 2 is how you dip your toes in,” Strickler says. “ISO is how you can take all those great controls you've done for SOC 2, put a program over them, and make them a more formal part of your organization.”

How to simplify SOC 2 and ISO 27001 compliance
Organizations can streamline SOC 2 and ISO 27001 compliance by adopting a coordinated approach where much of the work counts double. Strike Graph’s platform offers an efficient way to do this.
 “By joining frameworks together at the control level, we’re able to provide our customers with a platform to essentially design their own control environment,” says Micah Spieler, Chief Product Manager at Strike Graph. “We know every company is different; we know that every company uses different technology, collects different data, and has different user requirements. Having that flexibility at the control level, where the controls operate as the glue, you're not trying to match criteria. You're trying to figure out which criteria the control itself works to satisfy.”
“By joining frameworks together at the control level, we’re able to provide our customers with a platform to essentially design their own control environment,” says Micah Spieler, Chief Product Manager at Strike Graph. “We know every company is different; we know that every company uses different technology, collects different data, and has different user requirements. Having that flexibility at the control level, where the controls operate as the glue, you're not trying to match criteria. You're trying to figure out which criteria the control itself works to satisfy.”

How to bundle ISO 27001 and SOC 2 compliance
The achievement of either framework is what’s key to building customer trust. With Strike Graph, we break down the complex ISO 27001 and SOC 2 requirements into manageable steps and we advocate for a risk-based approach to establishing your security program regardless of framework so you know your business is protected.
Our approach supports SOC 2, ISO 27001, and many more frameworks because the risks, controls, and guidance we provide are all built to fit your organization's needs. Everything you need — from gap analysis and task assignments to progress updates and audit documents — is organized and easily accessible from your dashboard. Our innovative, easy-to-use compliance management platform adapts to your company’s specific needs, integrating with common business systems and infrastructure to automatically collect and validate evidence so you can prove compliance and drive the business forward.
If you want to learn how the controls between SOC 2 and ISO 27001 map specifically for your organization and what compliance framework you should go after, set up a time to chat with a Strike Graph compliance expert. Using Strike Graph there’s no need to re-map or guess where your gaps may be.
With Strike Graph, you can say goodbye to compliance stress.
ISO 27001 vs. SOC 2 FAQs
Here are some frequently asked questions about SOC 2 and ISO 27001 that can help you decide which is best for you.
Which industries benefit most from SOC 2 and ISO 27001 certifications?
Industries that handle sensitive information, such as healthcare, finance, IT services, and cloud providers, benefit most from SOC 2 and ISO 27001 compliance. These designations help enhance trust and demonstrate a commitment to data security. They are particularly valuable for organizations in highly regulated sectors.
How long does it take to get SOC 2 and ISO 27001 certified?
You can achieve SOC 2 certification in as little as 45 days for Type 1. SOC Type 2 takes two to six months or more. ISO 27001 certification can take anywhere from two months to two years or more. The length depends on the company’s complexity and maturity in security management.
What are the common challenges in implementing SOC 2 and ISO 27001?
Common implementation challenges are understanding and meeting the comprehensive requirements, allocating sufficient resources, and maintaining compliance. Both frameworks require time, effort, and expertise to implement effectively.
How do SOC 2 and ISO 27001 handle risk management?
SOC 2 and ISO 27001 emphasize risk management but approach it differently. SOC 2 focuses on risks across an entire organization. ISO 27001 is a comprehensive framework for identifying, assessing, and mitigating confidentiality, availability, and integrity risks.
What documentation is required for SOC 2 and ISO 27001 audits?
Both audits require documentation (policies, procedures, settings, and configurations) to demonstrate the controls are at least designed appropriately. For SOC 2 Type 2, the auditor selects samples for controls that occur more than once a year. ISO 27001 audits require documentation of a statement of applicability, evidence of ongoing monitoring and improvement of the ISMS, and tracking of non-conformities.
How often do SOC 2 and ISO 27001 certifications need to be renewed?
SOC 2 attestation audits are performed at least annually. After the initial certification audit, ISO 27001 certification requires a surveillance audit every year and a full recertification audit every three years.
What is the cost of achieving SOC 2 and ISO 27001 certifications?
The cost of achieving SOC 2 certification varies but ranges from $20,000 to $100,000, depending on the scope and complexity. Considering implementation, auditing, and maintenance expenses, ISO 27001 certification can cost between $50,000 and $200,000.
How do SOC 2 and ISO 27001 address third-party vendor risk?
Both SOC 2 and ISO 27001 address third-party vendor risk by requiring organizations to assess and manage their vendors’ security practices. This involves due diligence, regular assessments, and ensuring vendors meet security standards.
What is the role of continuous monitoring in SOC 2 and ISO 27001 compliance?
Continuous monitoring is crucial for both SOC 2 and ISO 27001 compliance. It involves regularly reviewing and assessing controls, identifying and addressing vulnerabilities, and ensuring ongoing adherence to security policies and procedures.
Can ISO 27001 and SOC 2 work together?
Yes, ISO 27001 and SOC 2 can work together. Implementing both provides a comprehensive approach to information security management and control effectiveness. Together, they cater to regulatory requirements and client expectations.
How do SOC 2 and ISO 27001 complement each other?
SOC 2 and ISO 27001 complement each other by covering varying aspects of information security. SOC 2 focuses on specific trust service criteria. ISO 27001 provides a broader, systematic approach to managing information security risks.
Is SOC 2 an alternative to ISO 27001?
SOC 2 is not necessarily an alternative to ISO 27001 but a complementary framework. Organizations may choose one or both depending on their needs, client requirements, and market presence.
Is SOC 2 or ISO 27001 a certification?
ISO 27001 is a formal certification of an organization’s ISMS. SOC 2 is an attestation report by an independent external auditor confirming that an organization meets specific trust service criteria.
Are there any tools that help with both SOC 2 and ISO 27001 compliance?
Yes, various tools assist with SOC 2 and ISO 27001 compliance. These tools offer risk assessment, policy management, control mapping, and continuous monitoring to streamline the compliance process for both frameworks.
How does SOC 2 compare with SOC 1 and SOC 2?
SOC 1, SOC 2, and SOC 3 reports serve different purposes and audiences. SOC 1 evaluates controls relevant to financial reporting. SOC 2 assesses security, availability, processing integrity, confidentiality, and privacy. SOC 3, similar in scope to SOC 2, provides a public report without detailed results. While SOC 1 and SOC 2 reports are restricted to specific stakeholders, SOC 3 is for broader public assurance.
.jpg?width=1448&height=726&name=Screen%20Shot%202023-02-09%20at%202.57.5-min%20(1).jpg)
%20(5).png?width=500&height=300&name=Untitled%20(350%20x%20200%20px)%20(5).png)

 Michelle Strickler, Lead Product & Compliance Experience Strategist at Strike Graph, says each standard can present challenges without proper understanding and guidance. She holds a Certified Information Systems Auditor (CISA) and Risk and Information Systems Controls
Michelle Strickler, Lead Product & Compliance Experience Strategist at Strike Graph, says each standard can present challenges without proper understanding and guidance. She holds a Certified Information Systems Auditor (CISA) and Risk and Information Systems Controls

 “By joining frameworks together at the control level, we’re able to provide our customers with a platform to essentially design their own control environment,” says
“By joining frameworks together at the control level, we’re able to provide our customers with a platform to essentially design their own control environment,” says 






