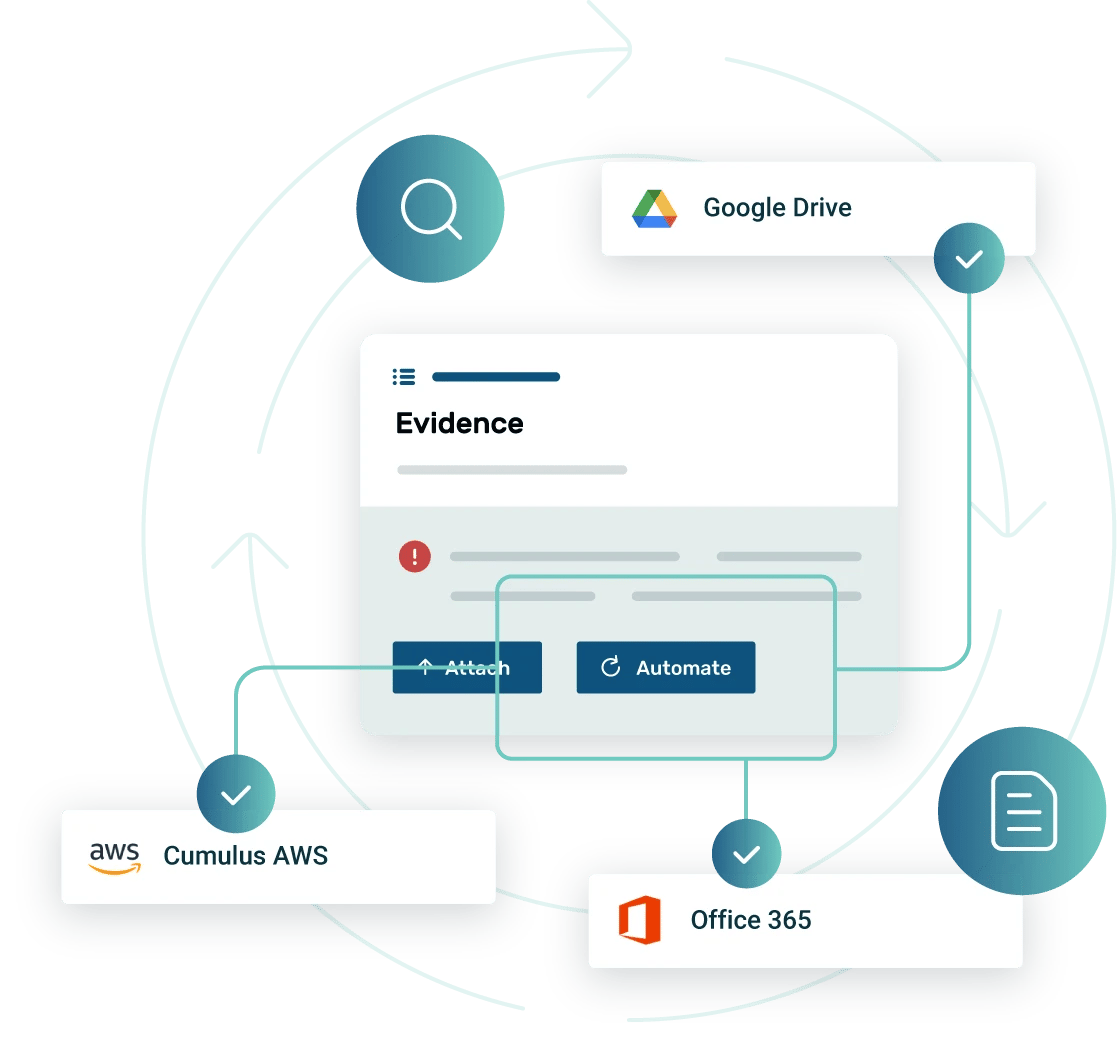
Automated evidence collection powered by precise integrations
Ensure continuous compliance across your entire technology ecosystem by leveraging automated evidence collection from over 300+ systems and tools.
With secure, zero-trust connections and flexible configuration options, you can collect compliance data from anywhere—without re-architecting your systems or adding security risks.

Unlike any other GRC platform, Strike Graph integrations meet you where your compliance data lives

Compliance is about building trust by capturing reliable data from within your technology ecosystem—regardless of the type of data or where it lives.
Strike Graph’s secure, AI-native compliance platform adapts to your architecture and keeps you continuously compliant, unlike any other GRC platform.
Whether you operate on AWS, Azure, or Google Cloud, our integrations collect precise, contextual evidence that maps directly to your controls and removes the burden for your team.
Enterprise-ready integrations for your core systems


Secure integrations with comprehensive coverage to power evidence collection

Protected data from end to end
All integrations follow zero-trust best practices with strict authentication, access controls, and encryption.

Comprehensive integration coverage
Connect to 50,000+ data points across cloud infrastructure, repositories, and collaboration tools. Evidence updates on a schedule that you define, keeping your program audit-ready at all times.
Automation that scales
Strike Graph automatically collects, validates, and refreshes evidence in real time. Verify AI alerts your team when action is needed, eliminating manual uploads and freeing engineers for higher-value work.
Integration options built for every environment
Strike Graph supports several options for integrations —giving you total control over how evidence enters your compliance program.
Third-Party Integrations
Out-of-the-box connections for standard enterprise systems like Google Drive, AWS S3, GitHub, Confluence, Jira, and Office 365. Automate complex data collection and customize evidence mapping across hybrid and multi-cloud environments.
Evidence API
Push evidence directly from any system into Strike Graph with our enterprise-grade REST API. Ideal for custom applications, legacy systems, or high-scale multi-cloud deployments that require continuous compliance monitoring.
“The Office 365 integrations has been great because it will just pick up whatever is in the folder – the most recent item. It’s made life so easy. If we didn’t have the integrations through Strike Graph, it would at least double the collection time.”
"The most helpful aspect of Strike Graph is its ability to automate compliance processes and provide clear, actionable insights. It saves our team a significant amount of time and effort, allowing us to focus on other critical tasks."
"What I like best about Strike Graph is its user-friendly interface and automation of compliance processes, which save time and effort. The platform’s comprehensive coverage of various compliance frameworks and its continuous monitoring capabilities make maintaining cybersecurity compliance straightforward and efficient."
“A game-changer for scalable compliance management. Strike Graph offers a highly intuitive interface that simplifies the journey to compliance."
Build and configure secure integrations faster with AI Security Assistant
Strike Graph’s AI Security Assistant for Integrations brings a revolutionary new level of intelligence to compliance automation.

The AI Security Assistant interprets API documentation, evidence requirements, and control mappings, enabling it to automatically generate the configurations or API routes for any integration — transforming what once took hours into minutes.
With built-in validation safeguards, every code snippet is reviewed before execution, ensuring automation that’s both fast and secure.
3 simple steps: How Strike Graph's automated evidence collection and integrations work
Grant secure access
Configure collection
Automate compliance
We don’t stop with smart integrations

Verify AI intelligence closes the loop.
Each time evidence is collected, Verify AI validates the completeness, accuracy, and alignment with your control framework in real-time, providing you with pre-audit readiness and continuous assurance.
List of Strike Graph integrations
Strike Graph integrates with the tools you already use, eliminating siloed workstreams and automating evidence collection so compliance runs seamlessly in the background.
Simplify compliance with secure, low-friction integrations.
Strike Graph integrations unify automation, security, and flexibility—helping enterprise teams streamline evidence collection, maintain audit readiness, and scale compliance effortlessly.

.jpg?width=1448&height=726&name=Screen%20Shot%202023-02-09%20at%202.57.5-min%20(1).jpg)
%20(5).png?width=500&height=300&name=Untitled%20(350%20x%20200%20px)%20(5).png)







