Stay ahead of the competition with ISO 27701.
Strike Graph makes it easy to strengthen privacy protections — and prove you’re GDPR and CCPA compliant — with the ISO 27701 add-on.
As privacy protections evolve, it’s essential to stay ahead of the curve.
ISO 27701 support
is tough to find.
Because the ISO 27701 privacy add-on is so new, there aren’t many platforms that offer support.
Strike Graph
has you covered!
We can help you add ISO 27701 to an existing 27001 certification or facilitate both for you, saving time and money.
Why ISO 27001 matters.
ISO 27701 is an international standard for privacy management, augmenting ISO 27001 with a focus on data protection. It helps organizations align with privacy regulations like GDPR and CPRA, demonstrating their commitment to handling personal data responsibly. This certification is vital for businesses operating globally, offering a framework to meet diverse privacy standards and bolstering consumer trust in data privacy practices.

-min.png?width=2000&height=900&name=Rectangle_20451_20(1)-min.png)
Strike Graph is your guide to cutting-edge privacy protections.
Stay ahead of the competition.
Strike Graph can help you get your ISO 27701 privacy add-on now, while your competitors are still wondering what it’s all about. It’s a great way to show your business partners and customers that you’re serious about protecting personal information and prove that you’re GDPR and CCPA compliant.
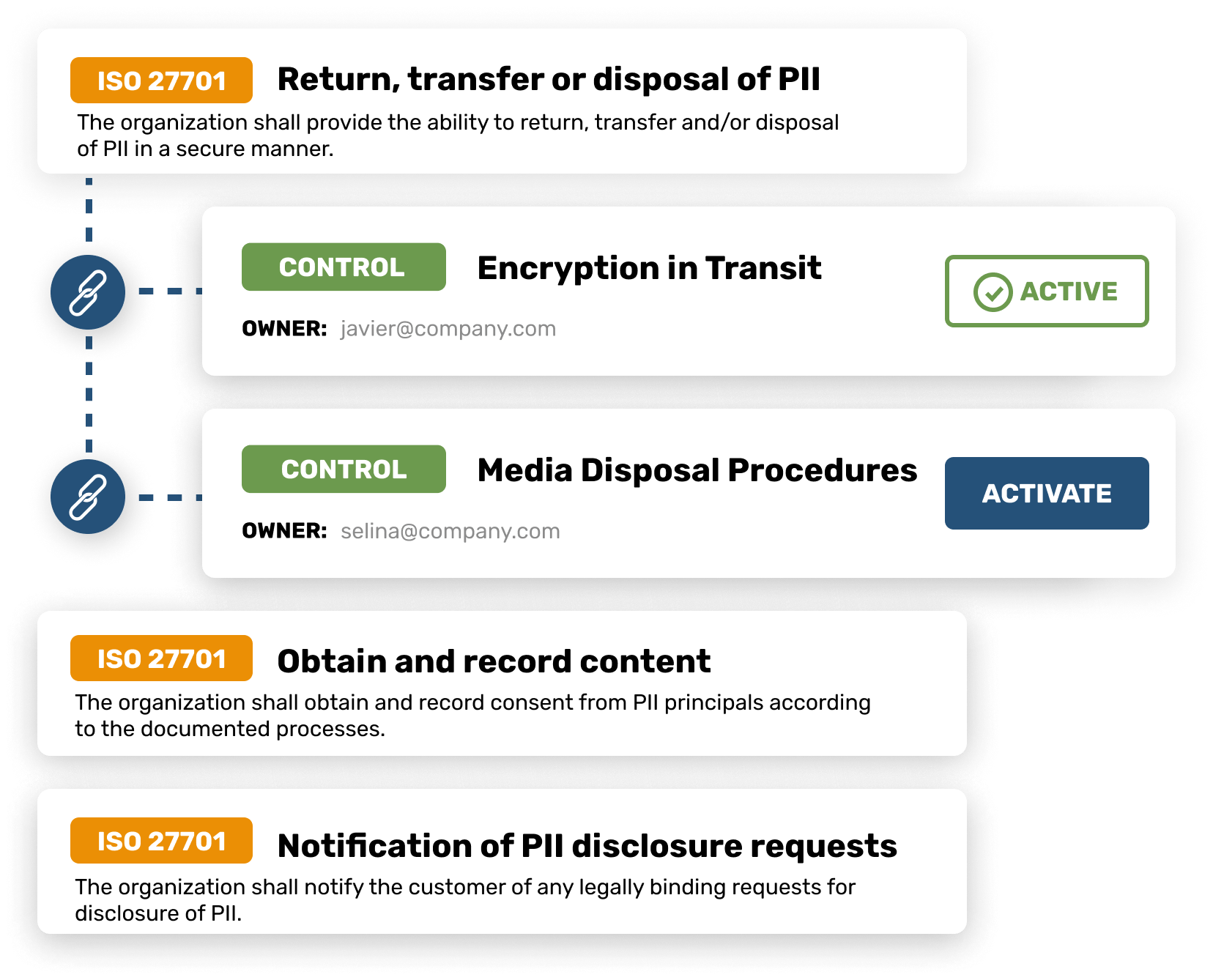
ISO 27701-specific templates
With Strike Graph, there’s no need to waste time figuring out unfamiliar ISO 27701 requirements. Use our extensive library of policy templates and pre-loaded controls — or, customize them to fit your exact needs.
.webp?width=1184&height=844&name=Policy%20Template%20(1).webp)
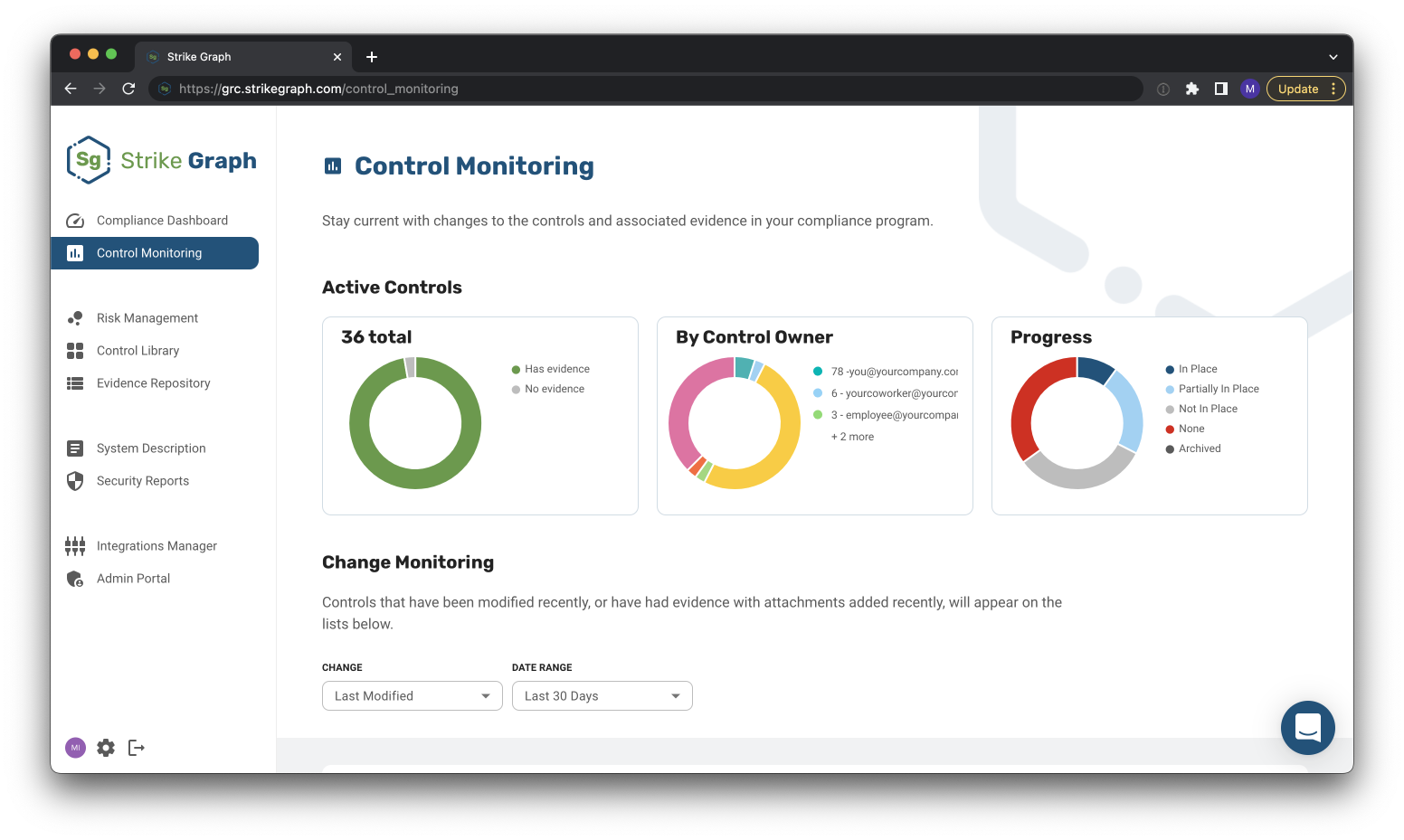
All your security certifications in one place
Strike Graph lets you apply controls across multiple frameworks, saving hundreds of hours of time when you need to add a security certification. We support SOC 2, ISO, HIPAA, PCI DSS, GDPR, and CCPA.
Packed with
useful features
penetration testing
Complete an initial risk assessment to identify security gaps.
Assign controls to each of your risks.
Pass your audit and receive ISO 27701 certification!
See what our customers have to say





Say goodbye to compliance stress
The team at Strike Graph is very hands-on, making my job a lot easier. From SOC 2 to ISO 27001, compliancy can be confusing, but Strike Graph provides the confidence that I have set my team up for success. Read more on G2.com
— Ben W., partnerships and growth specialist
Strike Graph has quickly become core to our compliance efforts
The platform makes managing your controls and evidence so easy, especially if you have multiple compliance frameworks you're working within (i.e. SOC2, HITRUST, ISO, etc.) Read more on G2.com
— Executive sponsor, Information technology and services
Strike Graph is your partner in compliance …
Strike Graph is your one-stop shop to get your security audits going and completed in half the time. There are file repositories for security audits, automated security questionnaires, evidence repository, and great support from the customer success team. Whether you need evidence of HIPAA, SOC 2, or ISO, you're in the right place. Read more on G2.com
— Administrator, information technology and services
Find out why hundreds of companies turn to Strike Graph for information security.
ISO 27701: Dig into the details.
ISO 27701 may be an add-on, but it covers a lot. Read on for answers to all your questions.
What is ISO 27701?
ISO/IEC 27701:2019 is one of the many standards published by the International Organization for Standardization (ISO). The organization has developed over 24,090 standards, ranging from environmental to information technology. ISO 27701 is part of the ISO 27000 family of standards, co-owned by ISO and the International Electrotechnical Commission (IEC). Its security techniques are an extension to ISO/IEC 27001 and ISO/IEC 27002 for privacy information management.
The new ISO 27701 standard, created for use by anyone responsible for PII in any sort of organization, was designed as the framework for demonstrating GDPR compliance. Prior to ISO 27701, companies could self-assess their adoption of GDPR to claim they were GDPR compliant, but there was no way of knowing for sure. ISO 27701 is an independently assessed certification of a company’s GDPR program. The standard shows you how to design, set up, manage, and continually improve a privacy information management system (PIMS).
How does ISO 27701 relate to ISO 27001?
ISO 27701 is a privacy add-on to ISO 27001. ISO 27001 is a framework for an organization’s information security management system (ISMS). An ISMS establishes management processes by means of information security controls to address information and data security risks. Its focus on information security risk management and continuous improvement makes it the most widely recognized IT Security certification internationally.
ISO 27701 expands the ISMS and creates a privacy information management system (PIMS).
What is an information security management system (ISMS)?
An information security management system (ISMS) is a management framework of policies and procedures to keep sensitive and confidential information secure. An ISMS establishes a systematic approach to security through policies, procedures, processes, technologies, and systems. This approach is designed to manage information risks such as cyberattacks, data leaks, insider threats, hacks, or theft.
ISMSs accomplish a number of goals:
- Enable organizations to secure information in all its forms and increase their resilience to attacks
- Enable employees and partners to readily understand risks and embrace security controls in their working practices
- Help businesses respond to evolving security threats to the integrity, confidentiality, and availability of the data they handle
- Improve businesses’ cybersecurity cultures through an integrated approach that covers technology, people, and processes
What is a privacy information management system (PIMS)?
A privacy information management system (PIMS) enables you to meet the highest standards of transparency and responsibility when processing personal information. Privacy information management systems, sometimes referred to as personal information management systems, cover the methods an organization has for collecting, processing, storing, and destroying personally identifiable information (PII. PII is considered any data that can be used to specifically identify a person; it can include an individual’s name, address, birthday, phone number, email address, IP address, etc.
PIMSs have a number of benefits:
- Provide new controller- and processor-specific controls
- Establish a point of convergence between what could be two different functions
- Help organizations overcome the challenges of privacy and security
What are the specific requirements to become ISO 27701 certified?
Since ISO 27701 builds on ISO 27001, you will need to obtain ISO 27001 certification simultaneously with ISO 27701, or have prior ISO 27001 certification with an ANAB/UKAS accredited certification body.
The ISO 27701 audit requires organizations to declare applicable laws and/or regulations in its criteria for the audit. This is so the standard can be mapped to the many requirements of CCPA, GDPR, or other laws. To obtain certification, you need to implement an effective PIMS complying with the requirements of the standard. Once mapped, the ISO 27701 operational controls are implemented by privacy professionals and audited by internal or third-party auditors. If this audit results in comprehensive evidence of conformity, certification is granted.
How can my company maintain its ISO 27701 certification?
The ISO 27701 certification is maintained through a program of annual surveillance audits and is valid for three years, at which point your organization will have to undergo a recertification audit. In the meantime, your organization will need to conduct periodic risk assessment reviews as risks and threats evolve, as well as perform internal audit management reviews, taking corrective actions on nonconformities.
Additional Resources
Check out more helpful guides from the Strike Graph team!


Additional Resources
Check out more helpful guides from the Strike Graph team!
Looking for more information?
We’re happy to walk you through our ISO 27701 process. Just fill out the form below, and one of our experts will get in touch!
.jpg?width=1448&height=726&name=Screen%20Shot%202023-02-09%20at%202.57.5-min%20(1).jpg)
%20(5).png?width=500&height=300&name=Untitled%20(350%20x%20200%20px)%20(5).png)


